News & Blogs
-

Deep Fake Scam
A finance worker is victim to a sophisticated deepfake scam, resulting in a loss of $25 million.... -

-

World Record Ransom Payment
Breaking a world record is usually associated with a fantastic acheivement but not in this case....... -
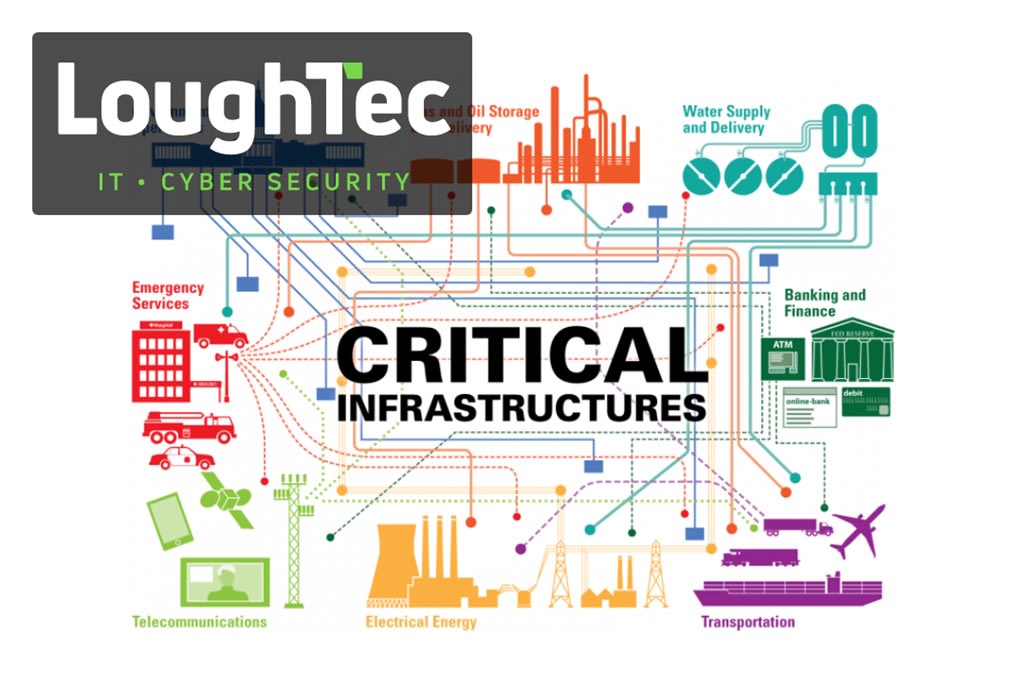
Data Centers are now Critical Infrastructure
Data centres in the UK are to be classified as critical national infrastructure now..... -

5 Cyber Incident Response Scenarios to Test Your Team
Ensure your business is ready for any cyber-attack by testing your incident response plan with realistic scenarios. Learn how to prepare your team and identify security gaps in our latest blog... -

Cyber Security trends of 2024
As we move through 2024, the landscape of cyber security has continued to shift rapidly, driven by emerging threats and technological advancements.... -

The Parallels Between Business Cyber Security & Family Safety
The analogy of treating your familys safety in a similar manner to how you handle cyber security for your business highlights the significance of care, attention, and protection in both personal and professional aspects of life.... -

Strengthening Domain Registration: Help Prevent BEC Scams
Controlling domain registration more effectively can certainly be a step towards making business email compromise (BEC) scams more difficult.... -

Understanding the Threat of Ransomware to Public Safety
Death by ransomware refers to a situation where a ransomware attack directly or indirectly leads to the loss of life.... -

How Cyber Defences Are Your Business’s Digital Dam
Building cyber defences can be metaphorically likened to building a dam in several ways:... -

Staying Competitive With Cyber Security Training
If you do not take cyber defence seriously, theres a high likelihood that your competitors will.... -

Understanding Phishing: A Critical Cybersecurity Threat
In todays digital age, cyber threats like phishing pose significant risks to organisations of all sizes.... -

The Power of AI in Cyber Security
Artificial Intelligence (AI) is already significantly impacting cyber security, and its role is expected to continue to evolve.... -

Understanding Cyber Crime Risks for Small Businesses
The chances of a small business falling victim to cyber-crime can vary widely depending on various factors, including the industry, the size of the business, the cyber security measures in place, and the specific threat landscape.... -
How Small Businesses Fall Victim to BEC Scams
Small businesses are susceptible to Business Email Compromise (BEC) attacks due to several factors, including their reliance on email communication, potentially limited cyber security resources, and a lack of awareness about the sophistication of the... -

Future Trends of the Dark Web
Predicting the future of the dark web is challenging, as it is an ever-evolving and dynamic part of the internet.... -

Preventing BEC Scams with Domain Registration
Controlling domain registration more effectively can be a step towards making business email compromise (BEC) scams more difficult.... -

Why Cyber Security Matters For Every Business
Believing that a cyber-attack will never happen to your business is a risky assumption.... -

Why Multi-Factor Authentication Matters
Multi-factor authentication (MFA) is a highly effective security measure that significantly reduces the threat of account takeover, but it doesnt completely solve the problem.... -

The Impacts of Cyber Crime
Cyber-crime can lead to a range of detrimental consequences, and the severity of the impact depends on various factors, including the nature of the attack, the target, and the attackers motivations... -

Why Paying a Ransom Fee Isn’t the Solution
When faced with a cyber attack demanding ransom, its crucial to understand why paying it may not be the best choice....





